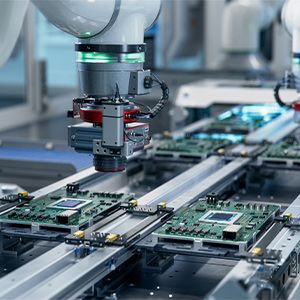
Choosing a VPN For
Industrial Applications
Post By: Ryan King On: 29-11-2018 - Automation & Control
Industry 4.0 has seen the rise of the Industrial Internet of Things (IIoT) which allows multiple devices to connect and communicate over the internet. This rise in connected devices has increased security concerns from many manufacturers around the world. Many manufacturers are looking at Virtual Private Network (VPN) solutions to tunnel their traffic and provide secure connectivity between their machines and other connected devices like servers.
VPNs are not new, they have been around for many decades. They have typically been used in office environments where businesses would have multiple offices and would require access to servers/devices in other locations, securely. However, manufacturers are starting to adopt VPNs within their factories and offices to improve the security of their connected devices.
What is a VPN?
A VPN or Virtual Private Network is a service which routes network traffic through one or more servers using encryption to protect the data transmitted. There are three main types of VPNs currently being used by businesses.
IPsec VPNs
IPsec is an industrial strength VPN which is highly flexible and configurable. It comprises three protocols, an Authentication Header (AH), an Encapsulating Security Payload (ESP) and an Internet Key Exchange (IKE). The authentication header adds a small packet of data to all requests made which contains a secure authentication token which either allows or disallows the traffic through the VPN. The encapsulating security payload provides message authentication and encryption while the internet key exchange provides key management and a protocol negotiation layer.
IPsec operates at the network layer (IP), this allows IPsec to work with any protocol which works with IP. IPsec is widely available with many network hardware manufacturers like Cisco, Juniper and Ubiquiti. IPsec can be more difficult than other VPN types to configure and requires an experienced technician to keep it running.
IPsec has been the choice for many businesses looking for high-security connectivity that can handle large volumes of traffic.
OpenVPN
OpenVPN is a general purpose network-to-network or computer-to-network VPN. While similar in functionality to tunnel mode ESP, OpenVPN is easier to configure and more lightweight than IPsec. OpenVPN is a program which runs on Unix/Linux, Windows and Mac systems which uses TLS (SSL) for key and configuration negotiation. OpenVPN can be configured to use shared keys which while are simpler are less secure. When using certificates with OpenVPN, you can achieve a very robust and secure VPN solution, perfect for maintenance engineers.
OpenVPN is simple enough that most businesses do not require a dedicated engineer to manage, provision and maintain the VPN. Because the VPN uses a user mode application, it usually cannot withstand high traffic volumes.
SSL VPN
SSL VPNs link a single computer to an application gateway on a corporate network. SSL VPNs utilise the client's web browser as the interface which means that additional software and configuration is not required. This drastically reduces the time to set up new clients and does not need experienced professionals to setup.
The main disadvantage of using an SSL VPN is that only traffic which goes through the web browser is proxied through the VPN, leaving other applications and ports open to the insecure outside network.
How do VPNs Work?
VPNs work by tunnelling/proxying your traffic through another computer, network or server through data encryption and isolation. If you are requesting data from sources that are not on the other end of the VPN tunnel, the VPN will request that data without the added security of the network.

What to Look For in a VPN?
When looking for a VPN solution, it is vital that you explore all of the advantages and disadvantages of the different systems on offer.
A hosted VPN solution utilities a central datacentre which hosts you VPN host that you clients then access. This host then routes the traffic throughout the network. A hosted solution does not require your business to manage the VPN. However, you will want to choose a reputable provider which you can trust with your data. Some providers will offer low prices, while they sell high-level traffic data anonymously with other businesses.
Hosted VPN solutions typically come with bandwidth limits which many businesses will exceed very quickly. This can result in higher than expected bills for going over your bandwidth allocation.
Traditional VPNs rely on your business hosting the hardware and software to manage the VPN. Using traditional VPNs means you will need an experienced professional to handle provisioning, maintenance and security in-house.
Traditional VPNs rely on your network, hardware and your internet connection speed. If your business is using a leased line, you are guaranteed a minimum up and down speed which traditional internet lines vary depending on usage both on your network and the local exchange. This can cause issues for some businesses that require fast, reliable connections.
Both hosted, and traditional VPN solutions have their advantages and disadvantages. For most companies, it comes down to four key areas, speed, security, cost and technical requirement. It is vital that in-depth research is done to find the right solution, and on some occasions, you may not always require a VPN.
Get More From Rowse Straight To Your Inbox